Detect design risk early
Spot insecure designs before they reach development. Compare each change against policies, frameworks, and threat models to catch weaknesses from the start.
From authentication-related changes to sensitive data flows: define what changes should be surfaced through application-specific policies.
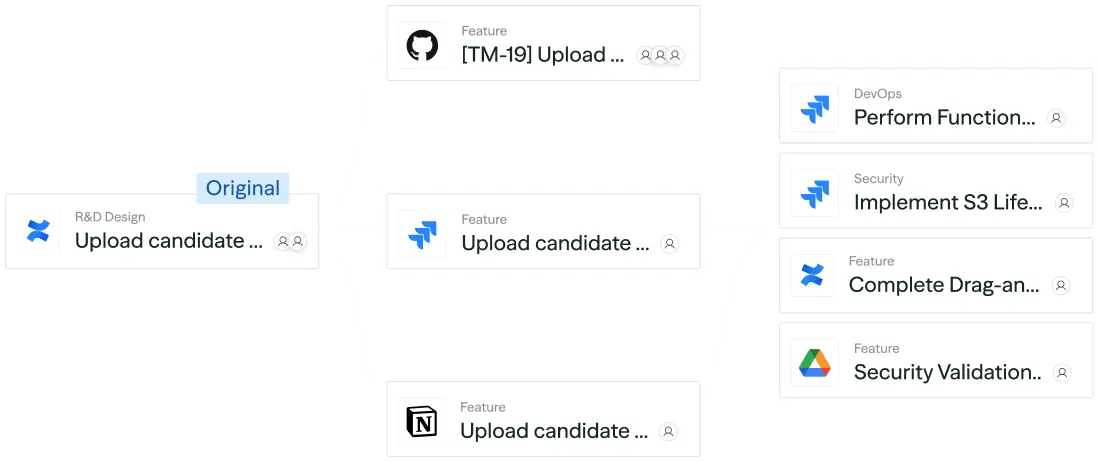
Gather design docs, tickets, architecture diagrams, code, pentest reports, and threat intel to maintain a live view of product, business, and security posture.
Map features and changes to relevant controls and threats. Score each one by likelihood, impact, and posture to set priorities.
Automatically route risks to the right people at the right time, with the rationale, next steps, and workflow triggers needed for fast resolution.
Connect seamlessly to the tools you already use to extract context, route insights to builders, and make secure-by-design a natural part of your development flow.
Catch risk in design, before you write a single line of code.
Identify and address design flaws before they turn into costly rework or late-stage fixes.
Ship faster and more simply with paved roads and fewer handoffs.
Direct effort with greater accuracy through automated risk scoring and prioritization.
Measure your coverage, adherence, and remediation metrics.
Quantify progress over time with live metrics on coverage and resolution.